E-Mail Signing Certificates

Don't Get Robbed!
During my 20 Years as an IT Consultant, one of my worst experience has been to witness data corruption from hackers that has damaged, even destroyed some companies. Techniques such as used through ransomware are constantly evolving and becoming more difficult to detect with every passing day.
Ever get a message from someone and learn it wasn’t from them? Make the mistake of opening an attachment, of not having the proper updated virus protection and you, as well as others in your organization may lose a lot of very important data.
A client owes you money? Email spoofers have been known to fake email addresses and have money deposited into their bank accounts. Email spoofing is what hackers do to get to you, your customers and friends. That’s where it starts, fake email addresses.
There’s a solution… A sure way to know if a message is real is if it’s sent with an authorized certificate signature. Tell your customers and friends all your messages use a signing certificate, that if your mail doesn’t have the signature symbol it’s not from you. It’s an inexpensive, easy way to protect everyone.
how it works...
there’s more,
encrypt your messages too!

Actual Email Message Sent To A Client 4/18/2020...
Guys,
There is something more you should know about signing certificates. More than ensuring mail received is from who it says, they also prevent those unauthorized from reading. Your message sent that was intercepted, modified for thousands of dollars to be deposit into a fraudulent account, a signing certificate would have prevented that.
For example…
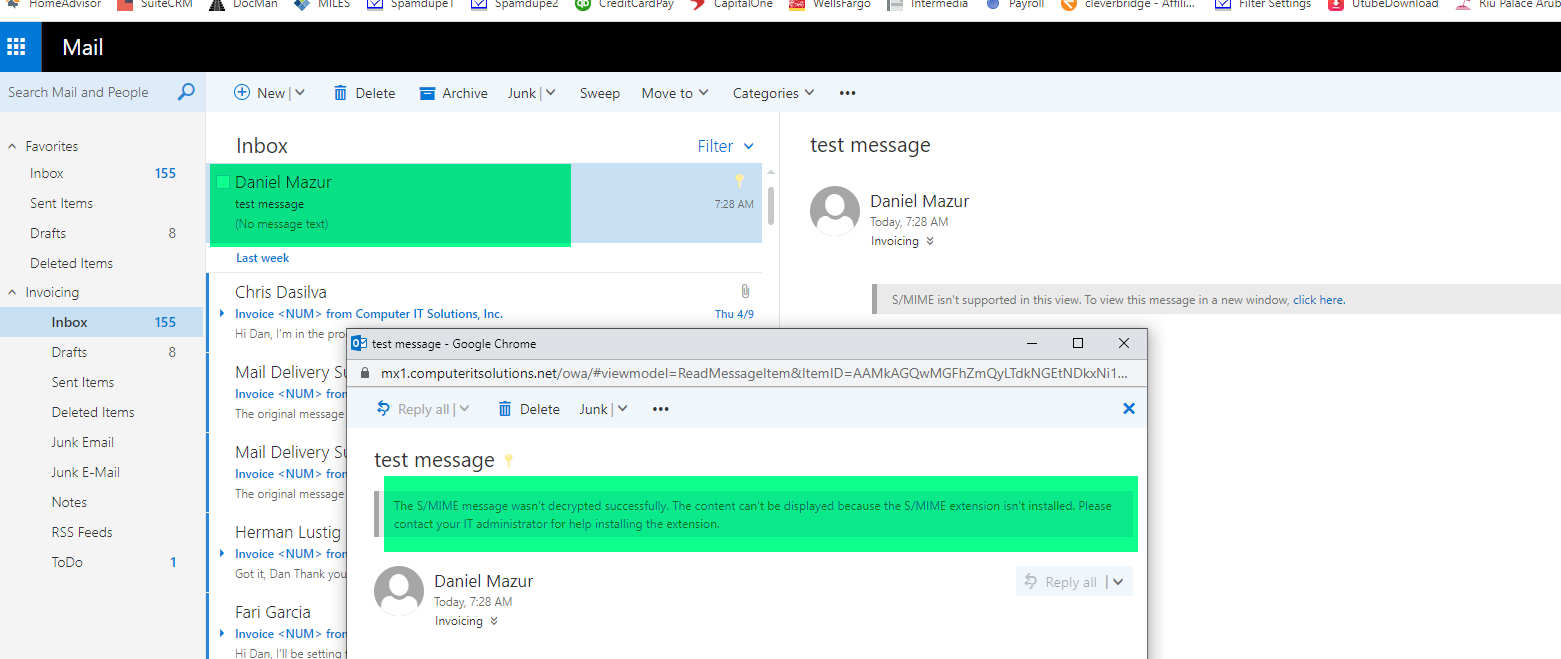
Look at the image below. I used my signing certificate to encrypt a test message sent from dan@computeritsolutions.net to another email account, invoicing@computeritsolutions.net . When I went to an offsite computer to read the message, I used my password and had access, but was unable to read any of my encrypted messages (see “test message” highlighted in green below). This is because the computer I accessed my email account on did not contain my security certificate.
Conclusion: If you need to prevent unauthorized access to mail, use signing certificates!
Click the link below, we’ll do all the work setting up the signing certificate for you, remotely or during a brief friendly visit to your home or office.


